EPB recovers the password to backups and password containers by checking various passwords to see which one matches the backup password. This can be compared to "attacking" the password, so attack is actually a task that is intended to find the correct password. A combination of attacks makes up a recovery pipeline.
NOTE: Recovering passwords is available only when using EPB for Windows OS.
There are two types of attacks available:
▪Dictionary: The task is based on searching the password in particular dictionaries (the dictionary is a text file, one word per line). You can use third-party password dictionaries, create your own dictionaries, or use the standard one provided by Elcomsoft.
▪Brute-Force: This type of attack allows checking all passwords in a given range by applying different combinations of symbols to see if they match the necessary password.
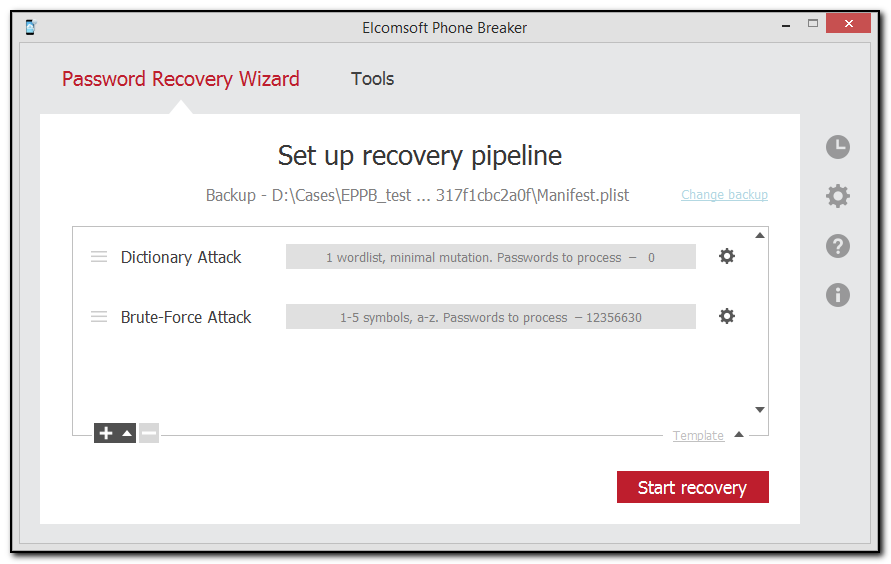
You can see the settings of the attack highlighted in grey, including the number of words to be processed during this attack. To change the settings of the attack, click ![]() next to the selected Dictionary or Brute-Force attack.
next to the selected Dictionary or Brute-Force attack.
The tasks are checked in the order they are listed, so you can create several tasks with increasing level of difficulty. For example, you can check simple combinations first, then the medium ones, and only after that difficult combinations, to save time if there is high likelihood that a simple password was used.
Additionally, you can use templates to save selected attacks or to load already existing attacks from a template.